The problem
Security Tools Are Fragmented
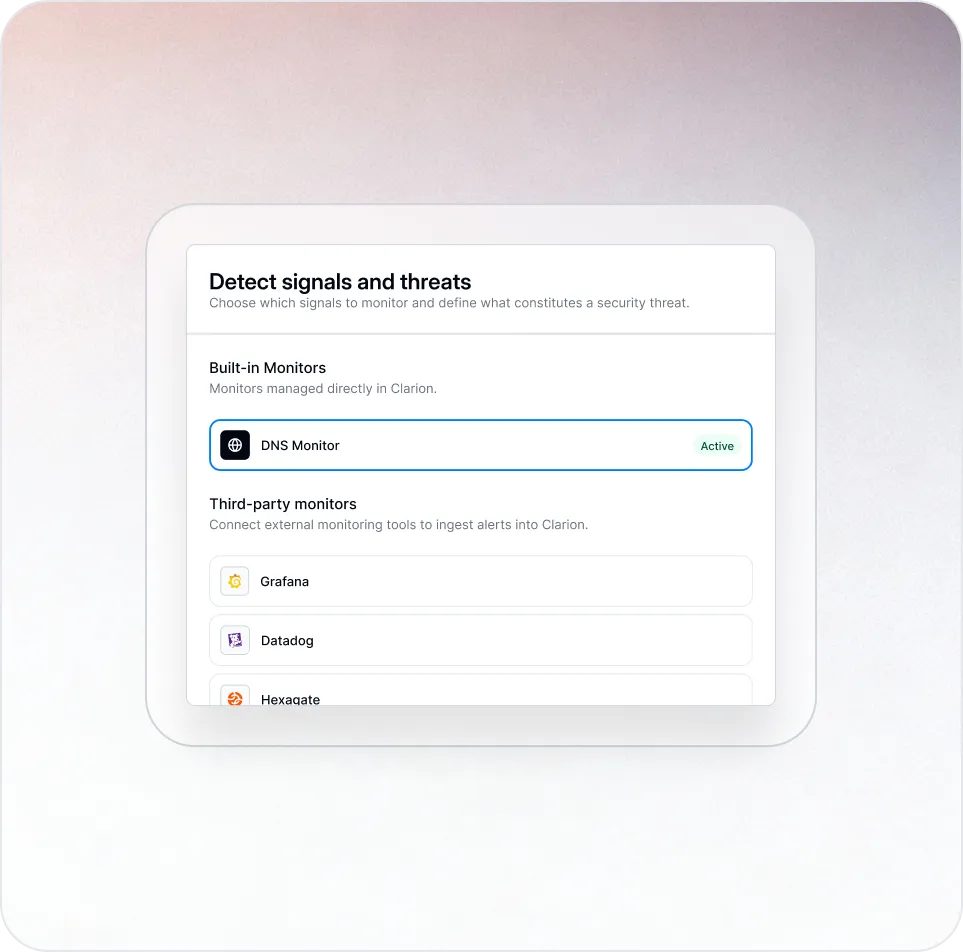
Modern infrastructure spans cloud systems, applications, identities, and third-party services.
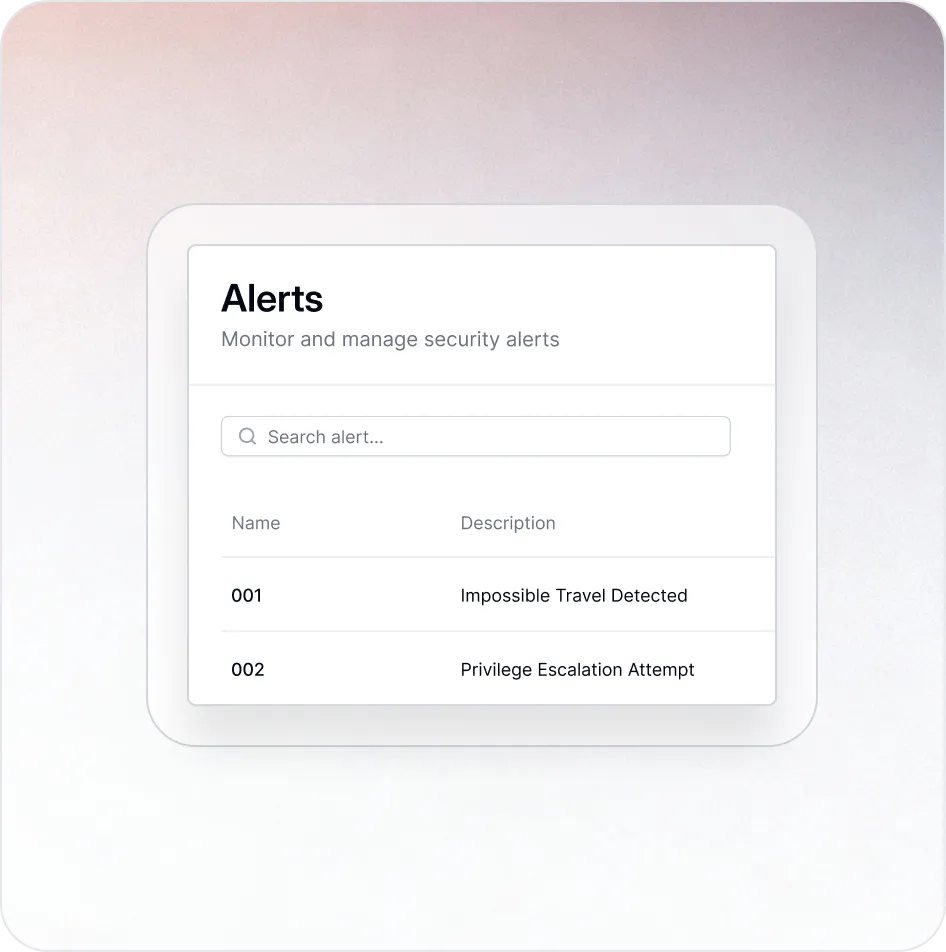
Each layer produces alerts, but those alerts are scattered across different tools and dashboards.
Security teams are forced to manually correlate signals before they can even begin responding.
















.png)

