Introduction
TRON is one of the most active Layer 1 blockchains, powering digital asset flows, stablecoin settlements, and content-driven protocols. Its architecture supports high throughput, consistent finality, and low transaction costs. These advantages also increase the complexity of ensuring system security.
The TRON Virtual Machine diverges from EVM behavior in ways that impact execution assumptions, resource modeling, and upgrade patterns. Developers who rely on Ethereum defaults often introduce state inconsistencies, failed assumptions, or unmonitored exposure.
Spearbit’s lifecycle security programs validate every layer of a TRON deployment. Our work spans architecture, implementation, operational readiness, and incident resilience. The objective is not limited to correctness. The goal is architectural clarity under stress.
Key Differences that Affect Security
Security design must begin with a clear understanding of TRON’s foundational mechanics.
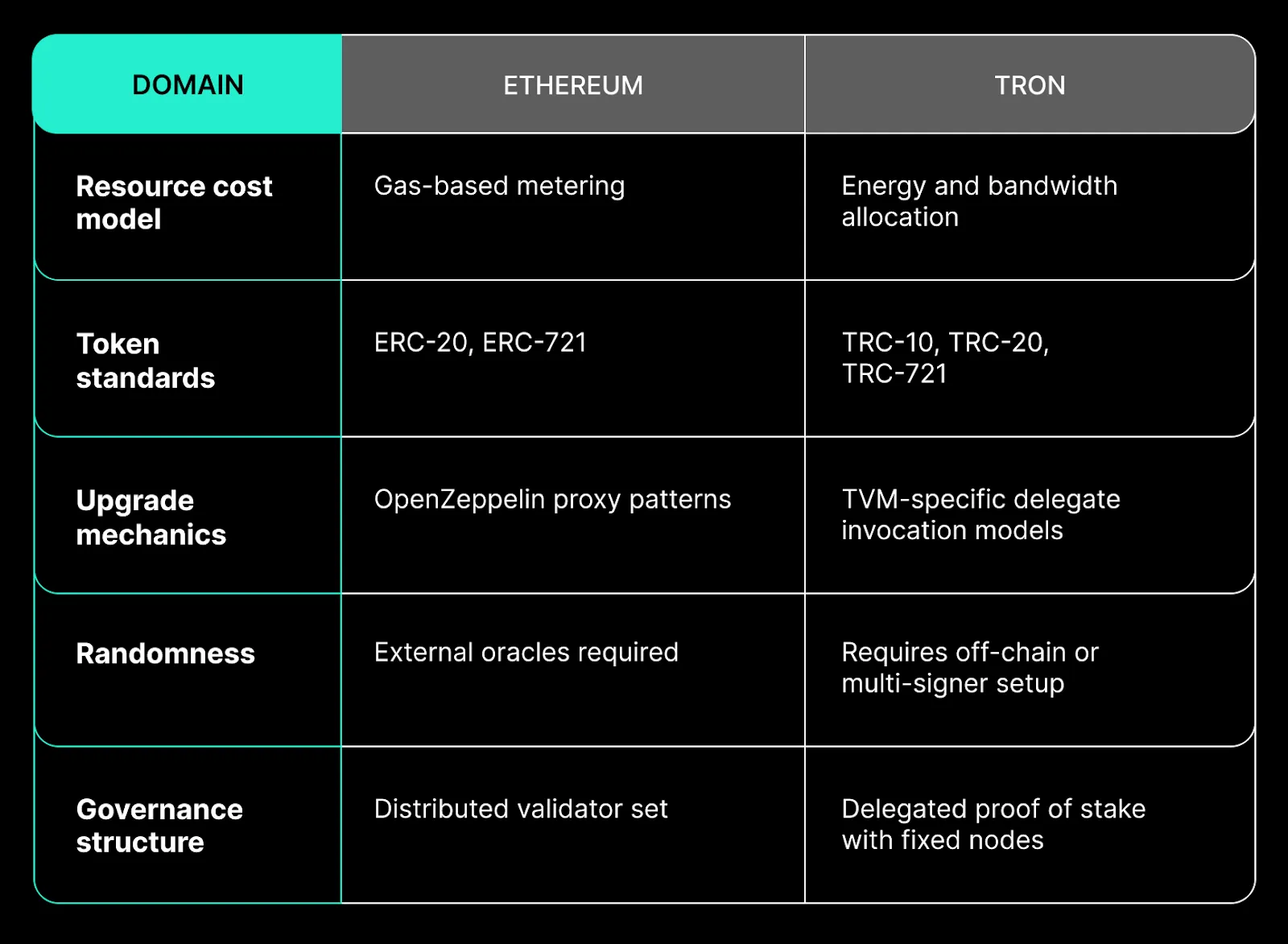
Security reviews that ignore these dimensions risk missing critical failure points.
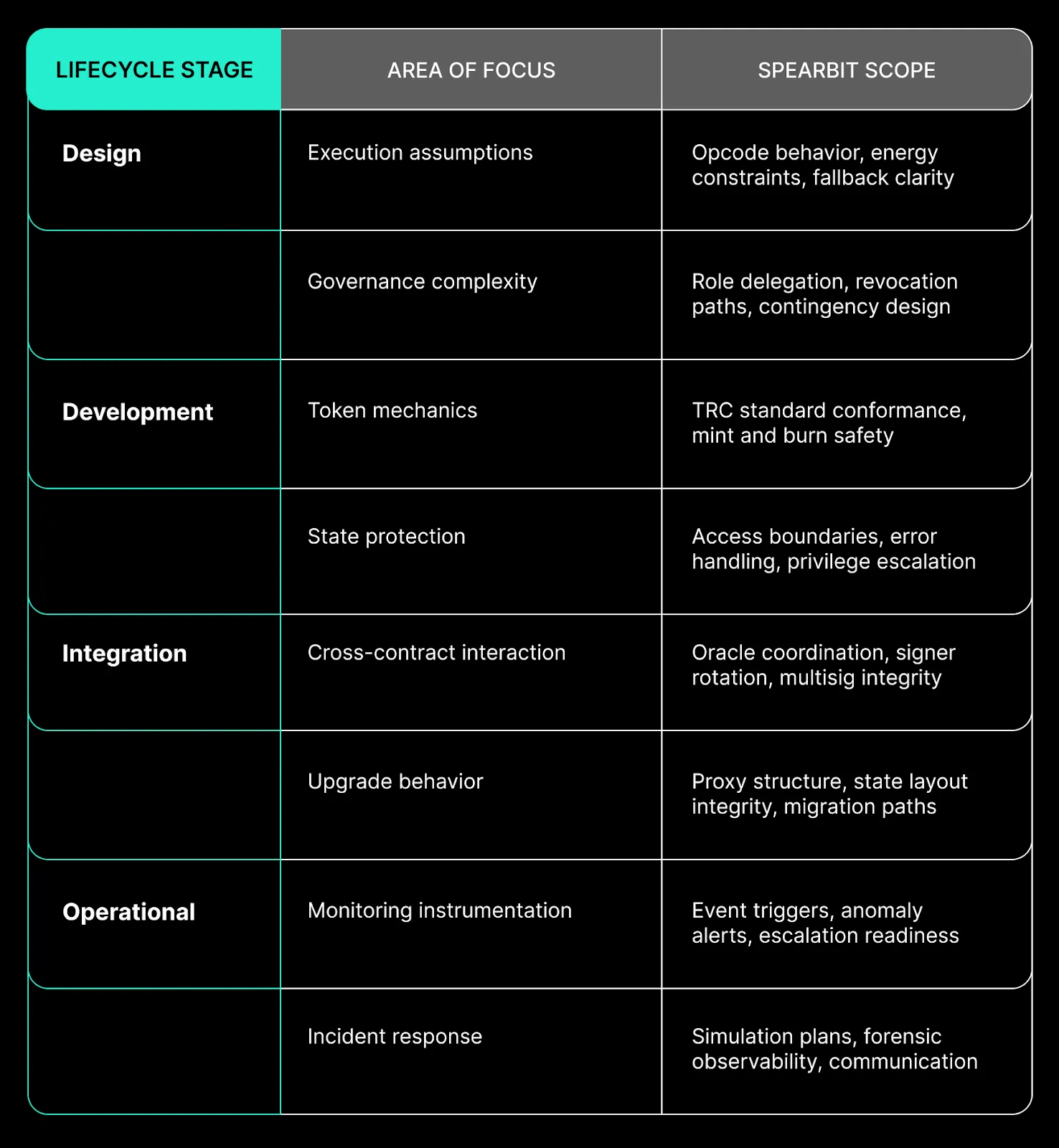
Security Across the Protocol Lifecycle
Spearbit engages at every phase of a protocol’s maturity. Each lifecycle stage introduces different risk types, requiring specialized validation.
Example: Oracle Failure from Resource Saturation
In a recent protocol audit, a decentralized exchange on TRON failed under high volatility due to energy constraints. The price oracle consumed nearly all available energy, leaving no margin for liquidation or slippage enforcement. Transactions silently passed without achieving intended state changes.
Conditions Observed
Oracle logic executed correctly under normal load. Under stress, energy depletion prevented full transaction completion without reverting. Users received no indication of failure.
Mitigation Strategy
- Energy profiling applied to external calls
- Circuit breakers installed for overuse scenarios
- Redundant pricing sources introduced with deviation tolerance
- Logging extended to capture partial transaction attempts
This scenario did not present through code review alone. Lifecycle testing and scenario simulation revealed the failure pattern and informed remediation.
Operational and Governance Considerations
Secure TRON deployments must treat access control as more than a modifier check. The delegated validator model introduces governance risk if revocation paths are unclear or misconfigured.
Spearbit evaluates:
- Multisig coverage for upgrade authority
- Role clarity across engineering and governance contributors
- Key custody models tied to validator and deployment responsibilities
- Contingency execution during coordination failure
We map responsibility across contracts, infrastructure, and organizational roles. Security is enforced through clarity, not reaction.
Post-Deployment Readiness
Effective monitoring is not just about logs. It is about signal fidelity and alignment with decision thresholds. TRON provides rich event hooks that can inform structured observability.
Spearbit integrates:
- Custom event mappings across privilege-changing operations
- Transaction filters tied to anomaly heuristics
- Predefined triggers for coordinated containment
- Postmortem readiness for incident reconstruction
Monitoring is not a standalone capability. It must be paired with incident command systems that translate signals into credible action.
How Spearbit Secures TRON Ecosystem Protocols
Spearbit delivers structured engagements that map to TRON’s operational and architectural landscape. We provide:
- Formal design-phase validation built around TRON-specific execution behavior
- Access control reviews that extend beyond contract modifiers
- Simulation of upgrade flows, state drift, and custody faults
- Integration audits across oracles, custodians, and deployment pipelines
- Incident command modeling tied to TRON governance constraints
Security in TRON is not only about smart contracts. It is about aligning execution logic, infrastructure configuration, and organizational governance into a system that can hold under pressure.
Begin a lifecycle security engagement with Spearbit to protect your TRON deployment before assumptions are tested in production. Contact us.




