Financial institutions are under siege by ever-evolving cyber threats, from sophisticated external attacks to risks lurking within their own walls. In fact, over 70% of financial services firms are now at risk of insider threats, and the average insider-related incident costs a staggering $16.2 million.
Compromised credentials are another major weak link. Recent data shows that stolen logins were the number one attack vector in recent years, accounting for up to 80% of web application breaches. These figures underscore a harsh reality: traditional perimeter-based security (the old “trust but verify” approach) is no longer enough.
Ultimately, banks need to embrace modern security architectures. Zero Trust and cloud security frameworks have emerged as the twin pillars of a strategy that can help financial institutions boost due diligence and protect customer trust.
Implementing Zero Trust in a Legacy Bank Environment
Zero Trust operates on the principle of “never trust, always verify,” treating every access request as potentially malicious.
Think of a traditional bank’s security like a house with a strong front door lock, but all the interior doors left open. Once an intruder gets inside, they roam freely. Zero Trust, by contrast, locks every internal door and requires continuous ID checks at each one. In practice, this means every user, device, and session must be explicitly authenticated and authorized in real time, and given only the minimum privileges necessary.
Key Zero Trust Principles
- Least-Privilege Access: Users have access only to what they strictly need.
- Assume Breach: Security teams operate as if attackers may already be in the network.
- Strict Segmentation: Internal barriers prevent free movement across the network.
Many banks still rely on aging core applications and networks that require significant upgrades or overlays to support granular access controls and continuous authentication.
The good news is that technology has matured, helping bridge this gap. Modern identity and access management tools and cloud-based security services can be introduced in stages.
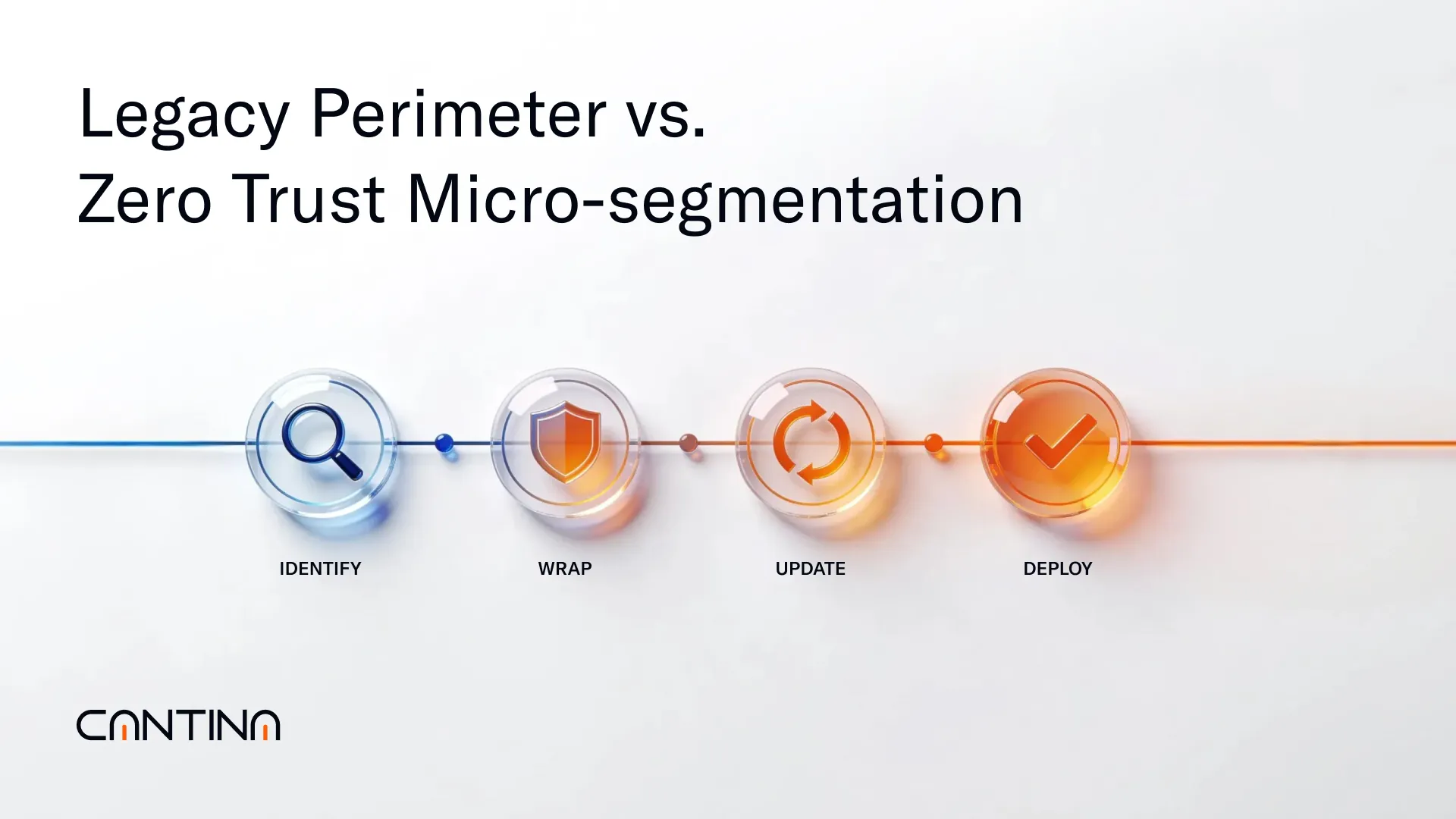
We recommend the following strategy for implementation:
- Identify high-value assets and critical data in legacy systems.
- Wrap them progressively with Zero Trust controls.
- Update protocols (e.g., adopting modern APIs for old systems).
- Deploy identity-aware proxies and institute monitoring around legacy apps.
Close collaboration between security teams, IT architects, compliance officers, and business leaders is essential during this transformation to avoid any security gaps.
A Zero Trust architecture dramatically reduces the blast radius of any breach. If a hacker or malicious insider hijacks a legacy credential, Zero Trust assumes nothing inside the network is trusted by default.
By continuously monitoring user behavior, the system can spot anomalies (such as a low-level employee trying to access a sensitive database) and cut off access immediately. Furthermore, by enforcing least privilege, even a compromised account can only do limited damage.
Securing Cloud Adoption Under Regulatory Scrutiny
As banks migrate workloads to the cloud, from customer-facing applications to back-end processes, regulators worldwide are watching closely.
It is not just an American concern. European and other global regulators have also issued cloud risk guidelines, requiring banks to maintain robust controls over outsourced cloud operations. In July 2024, for example, the U.S. Treasury and industry partners published a comprehensive set of best practices for secure cloud adoption by financial institutions. The message from regulators: Embracing the cloud doesn’t exempt banks from their responsibilities. If anything, it heightens the need for governance, security, and due diligence.
The reality is that cloud computing in finance is now widespread, with over 90% of banks reporting they run some form of data or operations in the cloud. However, maturity levels vary greatly. Many banks are still in early stages of cloud adoption, feeling their way through pilot projects or limited deployments. This learning curve, combined with regulatory pressure, means banks must “secure the cloud” by design.
Key Regulatory Concerns
- Third-party risk management
- Data privacy
- Operational resilience
- Compliance with financial regulations
Regulators have pinpointed challenges such as a lack of transparency from cloud providers (which complicates due diligence), shortages of cloud security skills, and even concentration risk (relying on a few big tech providers could threaten the whole sector) as obstacles the industry must address.
To meet these challenges and satisfy examiners, financial institutions should adopt a defense-in-depth approach for cloud deployments. This starts with strong governance.
You must know where your sensitive data is, who has access to it, and how it is protected. Banks should negotiate robust contracts with cloud providers that include provisions for security controls, audit rights, incident reporting, and compliance requirements (no more blindly accepting “take-it-or-leave-it” terms).
Additionally, many banks opt for a multi-cloud or hybrid cloud strategy, spreading applications across multiple cloud providers or combining them with private clouds, to avoid single points of failure and increase resilience.
Crucially, the technical security measures in the cloud must be as strong as, or stronger than, those in on-premise environments.
Best Practices for Cloud Security in Banks
- Multi-Factor Authentication (MFA): Implement granular access controls for all cloud logins, ensuring that stolen passwords alone can’t grant entry to sensitive systems. Notably, many recent breaches succeeded because accounts lacked MFA, allowing attackers to log in with compromised credentials.
- End-to-End Encryption: Encrypt sensitive data both at rest and in transit, coupled with strict key management so that even cloud service admins can’t access plaintext data.
- Regular Backups & Disaster Recovery: Prepare for cloud outages or ransomware. Backups should be stored securely (and ideally offline) to prevent tampering.
- Continuous Monitoring: Use tools to flag unusual activities, misconfigurations, or policy violations in real time across cloud environments. This might involve cloud security posture management and automated alerts for any changes.
- Privileged Access Management (PAM): Tightly restrict and monitor the use of high-level cloud admin credentials, as they are prime targets for insider abuse or takeover by attackers.
With these controls in place, banks can create a secure cloud architecture that meets regulatory requirements and significantly reduces risk. Importantly, many of these measures align with Zero Trust principles.
For example, MFA and continuous monitoring extend Zero Trust’s “never trust” ethos into the cloud, and least-privilege policies ensure that each cloud service or API has only the access it truly needs. Financial institutions that get cloud security right not only avoid regulatory penalties but also benefit from the cloud’s agility safely.
Insider Threats in Finance and How Zero Trust Helps
Insider threats, whether malicious employees, careless staff, or clever impostors using stolen credentials, represent one of the most dangerous threat vectors in finance.
Banks thrive on trust, yet insiders are trusted by default, which can be deadly. Studies show that over two-thirds of organizations feel vulnerable to insider incidents, and many have suffered multiple insider attacks in the past year.
Addressing insider threats requires a shift in mindset: trust no one, verify everyone, and watch everything. This is exactly where Zero Trust architecture shines. Zero Trust assumes that an attacker might already have a foothold inside your network, say, via a leaked VPN password or a malware-infected laptop, and it builds defenses accordingly.
Mitigating Insider Risk
- Continuous Scrutiny: Unusual behaviors (an employee downloading an unusually large amount of data, logging in at odd hours, or accessing systems they've never used before) trigger alarms or are blocked outright. Modern User and Entity Behavior Analytics (UEBA) tools often help distinguish benign anomalies from true indicators of compromise.
- Enforcing Least Privilege: Many organizations discover that users have far more access rights than necessary. By implementing strict privileged access management, a bank ensures that staff and service accounts can access only the resources essential to their roles. Crucially, all sensitive actions (like moving funds or downloading customer data) should require additional verification.
- Reducing Blast Radius: If an insider account is compromised by malware or an employee becomes malicious, their damage is limited by their restricted access.
- Preventing Unintentional Errors: Not every internal incident is the result of a disgruntled employee; many are mistakes or negligence. Zero Trust prevents damage from mistakes by compartmentalizing access. For example, if an employee’s device is infected with malware, micro-segmentation ensures it can’t spread freely to crown-jewel databases.
In this way, Zero Trust’s “always verify” approach creates a safety net beneath employees, catching errors before they become full-blown breaches.
Building Cyber Resilience and Trust Through Leadership
We believe that by openly discussing modern security architectures, we can foster a sustainable, safer financial ecosystem.
The future of financial cybersecurity will be won by those who prepare today.
The path to viral success in cybersecurity isn’t through fear-mongering, but through smart, intentional leadership: sharing knowledge, implementing best practices, and continuously adapting to stay one step ahead of threats. Contact us for more information, we'll available 24/7




